To reset forgotten password hard reboot your affected VM or bare metal server, press arrow key to skip boot timeout from grub, then press “e” search for line...
Uncategorized
How to configure HPE MSA controller IP manually using cli port
connect USB to your pc, open device manager and find COM port number, open putty, select serial, and change COM port number, "Baud rate" value may vary....
How to fix vCenter – no healthy upstream error.
I recently faced this issue when downgrading HPE Simplivity Node, we were using Center v7 U2, and we have to shut down everything for this host downgrade....
Installing Kali-Linux 64-Bit on Raspberry Pi-4
For the 64-Bit OS support we need to use Raspberry Pi 4I’m using Raspberry Pi 4 Model-B With * Gigs of RAM, A 4GB RAM model would work just fine.But First...
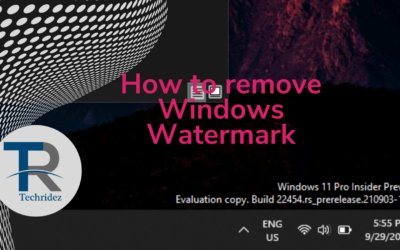
How to remove Windows Watermark
You may have faced this issue in Evaluation versions or Preview releases or OS you are not activated, it's very easy to remove this. using a free tool you can...
Disabling weak CBC ciphers in ssh Redhat
Today we will cover how to disable weak cbc ciphers in ssh server, after this you will pass cbc ciphers vulnerability.Environment Red Hat Enterprise Linux 8.x...
Subscribe For Instant News, Updates, and Discounts
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Curabitur arcu erat, accumsan id imperdiet et, porttitor at sem.