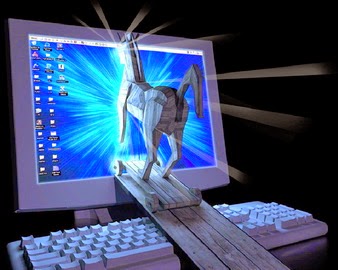
What is a Trojan Horse ?
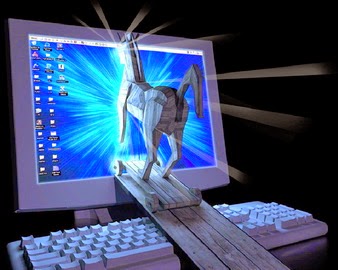 A trojan horse is used to enter a victim’s computer, granting the attacker ‘wrapped’ into a program meaning that this program may therefore have hidden fuctions that you are not aware of.
A trojan horse is used to enter a victim’s computer, granting the attacker ‘wrapped’ into a program meaning that this program may therefore have hidden fuctions that you are not aware of.
unrestricted access to the data stored on that computer and causing great damage to the victim. A trojan can be a hidden program that runs on your system without your information,
or it can be
Different types of trojans :
1) FTP torjans : These trojans open an FTP server on the victim’s machine that might store and serve illegal software and/or sensitive data, and allow attackers to connect to your machine via FTP.
2) Destructive trojans : The only function of these trojans is to destroy and delete files. This makes them very simple to use. They can automatically delete all the core system files on your machine. The trojan can either be activated by the attacker or can work like a logic bomb that starts on a specific day and time.
A destructive trojan is a danger to any computer network. In many ways, it is similar to a virus, but thedestructive trojan has been created purposely to attack you, and therefore is unlikely to be detected by your antivirus software.
3) Proxy trojans : These trojans turn the victim’s computer into a proxy server, making it available to the whole world or to the attacker alone. It is used for anonymous Telnet, ICQ, etc., to make purchases with stolen credit cards, and for other such illegal activities. This gives the attacker complete anonymity and the opportunity to do everything from YOUR computer, including the possibility to launch attacks from your network.
4) Denial of Servce (DoS) attack trojans : These trojans give the attacker the power to start a Distributed Denial of Service attack if there are enough victims. The main idea is that if you have 500 infected ADSL users and you attack the victim simultaneously from each, this will generate HEAVY traffic, causing its access to the Internet to shut down.
5) Security software disablers : These are special trojans, designed to stop/kill programs such as antivirus software, firewalls, etc. Once these programs are disabled, the hacker is able to attack your machine more easily.
6) Data-sending trojans : The purpose of these trojans is to send data back to the hacker with information such as passwords (ICQ, IRC, FTP, HTTP) or confidential information such as chat logs, address lists, etc. The trojan could look for specific information in particular locations or it could install a key-logger and simply send all recorded keystrokes to the hacker.
7) Remote access trojans : These are probably the most publicized trojans, because they provide the attacker with total control of the victim’s machine. Example : Back Orifice trojans. The idea behind them is to give the attacker COMPLETE access to someone’s machine, and therefore full access to files, private conversations, accounting data, etc. Some trojans can also automatically connect to IRC and can be controlled through IRC commands almost anonymously, without the attacker and the victim ever making a real TCP/IP connection.
Another question : How can I get infected ?
Generally, attack are being done through :
1) Infection via attachment ( of course emails : the most common way )
2) Infection by downloading files from a website (another common way )
Now most important thing, how to protect your network from trojans ?
Ok, if you think that anti-viruses are really helpful and they’ll protect your system and network from trojan attacks, then you are wrong. Anti-viruses just help us to some extent.
To effectively protect your network against trojans, you must follow a multi-level security strategy:
1. You need to implement gateway virus scanning and content checking at the perimeter of your network for email, HTTP and FTP – It is no good having email anti-virus protection, if a user can download a trojan from a website and infect your network.
2. You need to implement multiple virus engines at the gateway – Although a good virus engine usually detects all known viruses, it is a fact that multiple virus engines jointly recognize many more known trojans than a single engine.
3. You need to quarantine/check executables entering your network via email and web/FTP at the gateway. You have to analyze what the executable might do.
4. Do not open unsolicited attachments in email messages.
5. Do not follow unsolicited links.
6. Maintain updated anti-virus software.
7. Use an Internet firewall.
8. Securing your web browser.
9. Keep your system patched.
Good Luck !!
 A trojan horse is used to enter a victim’s computer, granting the attacker ‘wrapped’ into a program meaning that this program may therefore have hidden fuctions that you are not aware of.
A trojan horse is used to enter a victim’s computer, granting the attacker ‘wrapped’ into a program meaning that this program may therefore have hidden fuctions that you are not aware of.



0 Comments